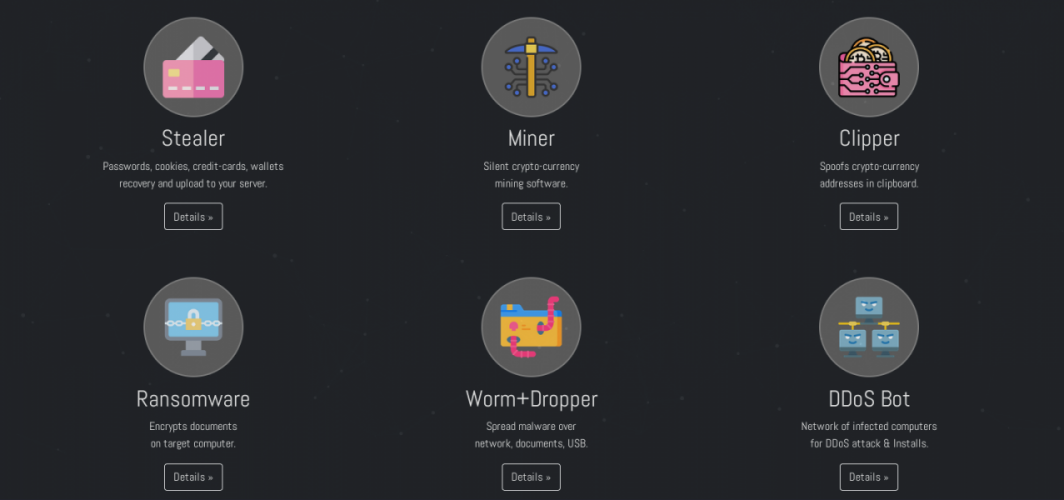
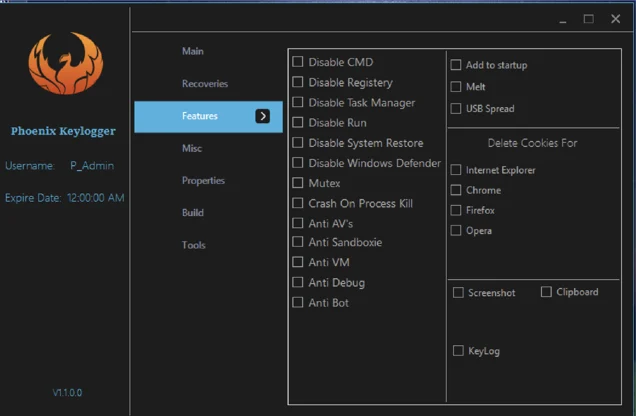
Stealers, access sales and ransomware: supply chain and business models in cybercrime | SideChannel – Tempest

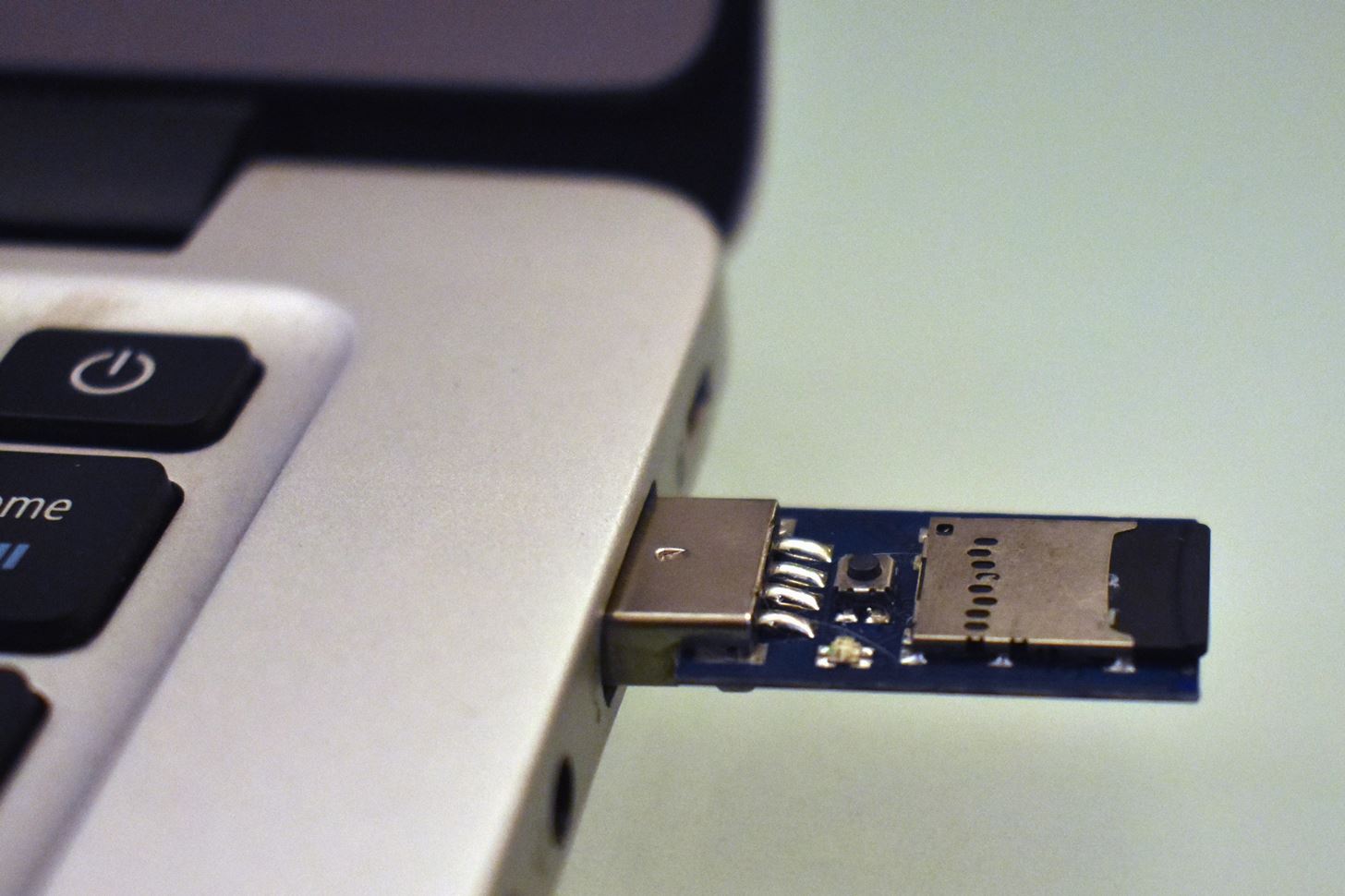
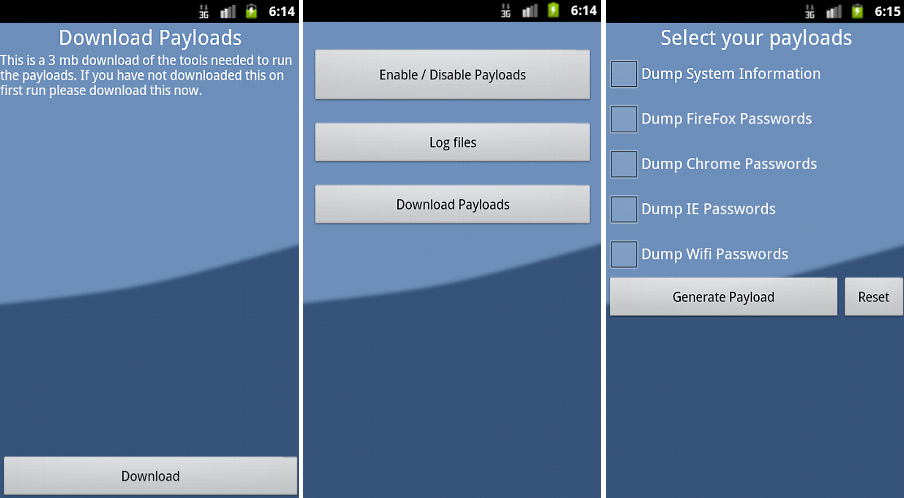
Implementation and Analysis of USB based Password Stealer using PowerShell in Google Chrome and Mozilla Firefox | Semantic Scholar
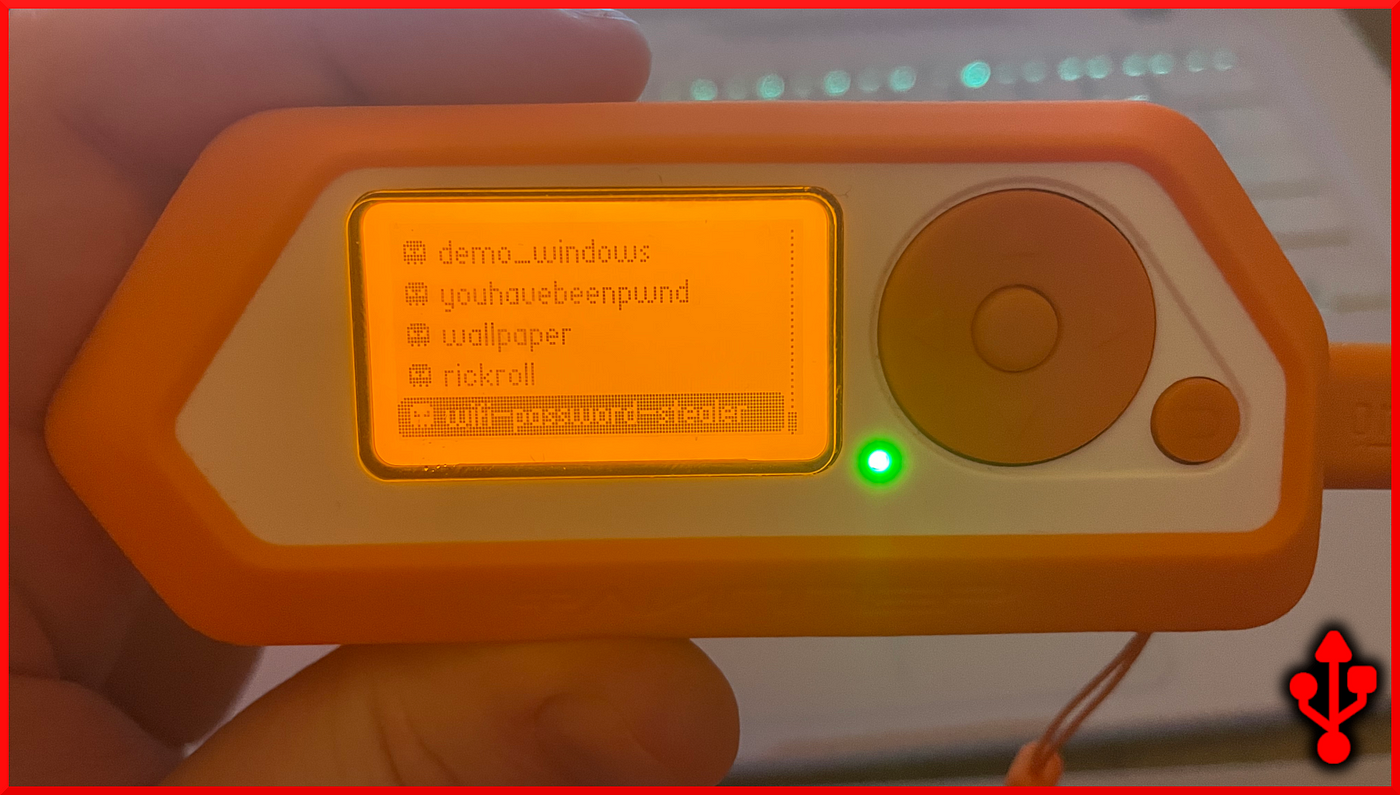
Implementation and Analysis of USB based Password Stealer using PowerShell in Google Chrome and Mozilla Firefox

Juice Jacking: How Hackers Can Steal Your Info When You Charge Devices - Hashed Out by The SSL Store™

Implementation and Analysis of USB based Password Stealer using PowerShell in Google Chrome and Mozilla Firefox | Semantic Scholar

Create a USB Password Stealer to See How Secure Your Info Really Is | Computer security, Usb, Best hacking tools

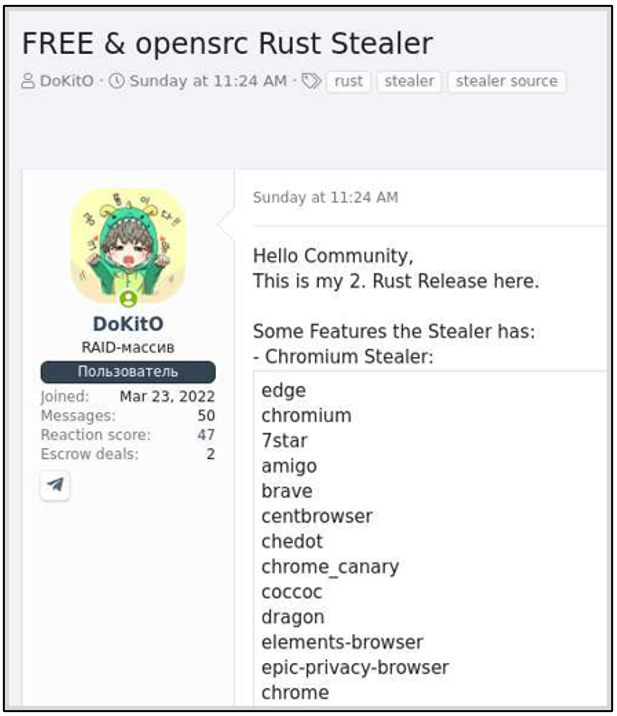
Metastealer – filling the Racoon void | NCC Group Research Blog | Making the world safer and more secure
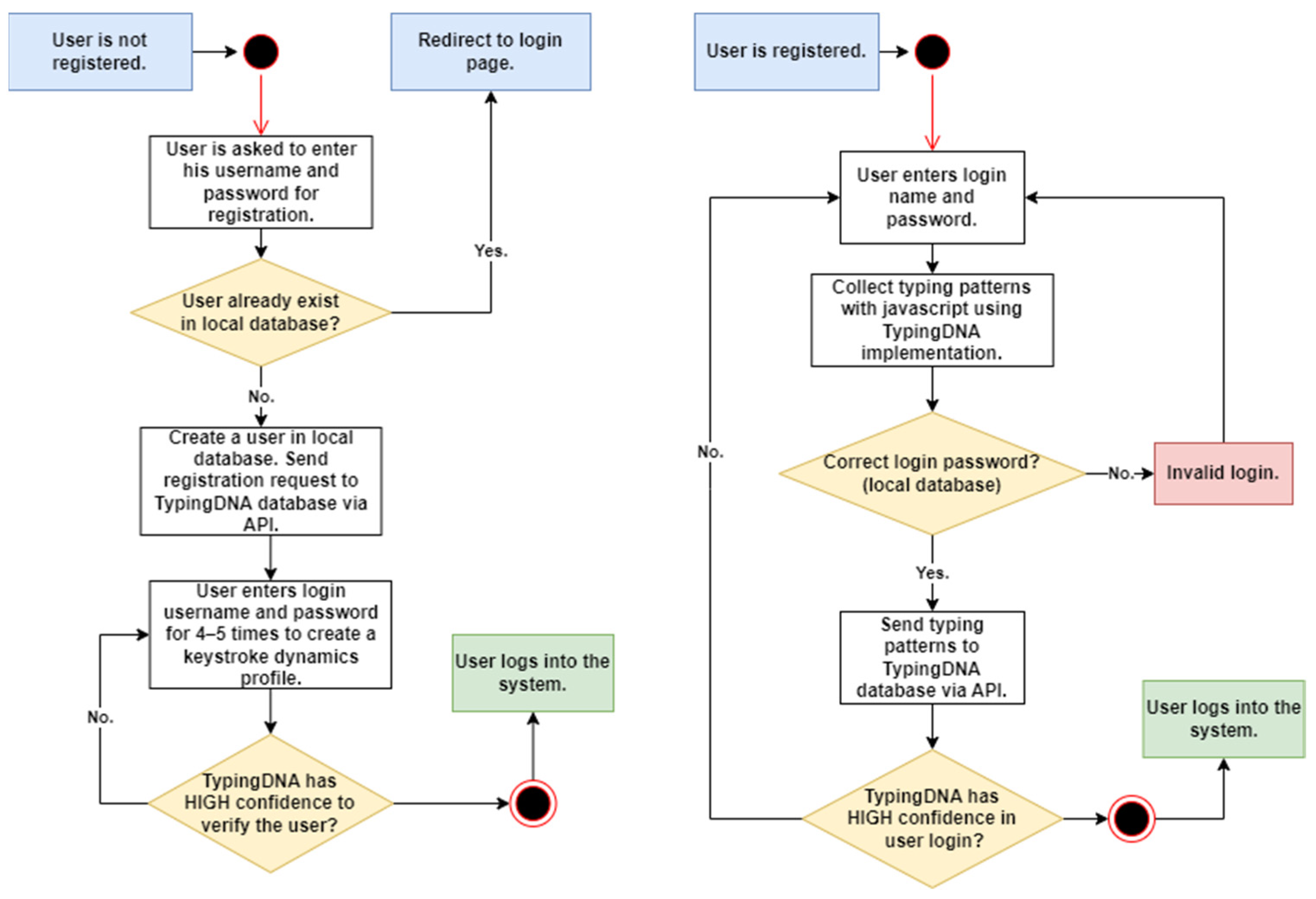
Electronics | Free Full-Text | A Deep-Learning-Based Approach to Keystroke-Injection Payload Generation







/cdn.vox-cdn.com/uploads/chorus_asset/file/23949203/226141_rubberDucky.jpg)